In Atlanta, telecom equipment recycling isn't a side task anymore. It's an operational control issue. In 2022, global e-waste reached 62 million tonnes, with small IT and telecommunication equipment contributing about 5 million tonnes, and only 22.3% was formally recycled according to global e-waste statistics. For an IT director, that reframes old routers, PBX hardware, switches, phones, and network gear as more than surplus. They are potential sources of data exposure, compliance trouble, and missed recovery value.
Most organizations don't struggle because they lack good intentions. They struggle because telecom gear sits in closets, MDF rooms, racks, storage cages, and decommissioned offices without a documented disposition path. Once that happens, the risks multiply fast.
The Growing Challenge of Telecom E-Waste for Businesses

Atlanta businesses replace telecom infrastructure more often than they used to. VoIP migrations, SD-WAN rollouts, Wi-Fi refreshes, fiber upgrades, and data center consolidations all create steady streams of retired hardware. The problem isn't just volume. It's that telecom assets often combine three hard issues in one item: embedded data, regulated disposal requirements, and recoverable commodity value.
A retired switch may still hold configurations. A PBX may retain call detail information. A firewall appliance may contain credentials, policies, and logs. If those assets leave a facility without controls, the company takes on avoidable risk.
Why storage is not a strategy
I've seen organizations treat obsolete telecom gear as a future project. That usually means equipment gets stacked, labels fade, and asset records stop matching reality. By the time disposal moves to the top of the list, no one is fully sure what has data, what still has resale value, or what has already dropped into scrap condition.
Practical rule: If a device ever processed traffic, stored settings, or connected to a managed environment, handle it like a data-bearing asset until proven otherwise.
That approach changes procurement, facilities, and IT conversations. Recycling becomes part of the lifecycle, not a cleanup exercise at the end.
What matters to an IT director in Atlanta
For most business environments, telecom equipment recycling has to answer four questions:
- Is the data gone: Not deleted. Not reset. Sanitized or physically destroyed.
- Is the chain documented: Every handoff should be traceable.
- Is the material handled responsibly: Downstream processing matters.
- Is there value to recover: Functional gear and high-grade components shouldn't be treated the same way.
Those trade-offs are where experienced ITAD planning makes a difference.
Defining the Scope of Telecom Equipment Recycling
Telecom equipment recycling covers a wider asset range than many inventories show. If the device supports voice, data, routing, connectivity, wireless coverage, or network power, it likely belongs in the telecom stream.
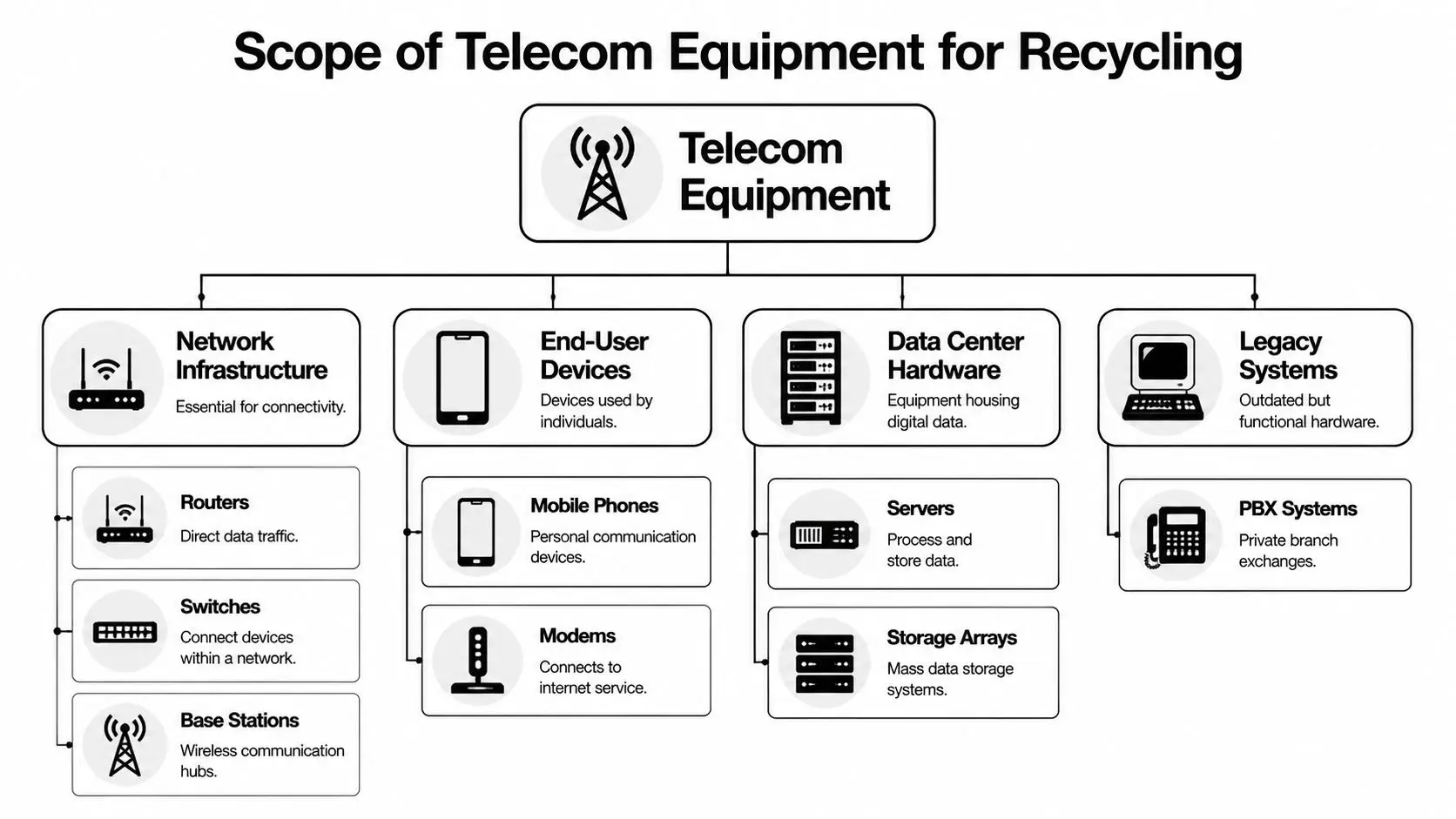
Core network infrastructure
This is the equipment most IT teams think of first. It includes routers, switches, firewalls, wireless controllers, modems, access points, and telecom transport gear. In some environments, it also includes carrier-grade hardware, base station components, and edge devices deployed across multiple sites.
These assets matter because they often contain configuration files, firmware, credentials, and network maps. Even when they look like simple appliances, they can still be data-bearing.
End-user and communications hardware
Desk phones, VoIP phones, conference phones, mobile devices, and call-handling equipment often get overlooked. So do devices tied to contact centers, branch offices, and field operations. They may not have the same resale profile as a core switch, but they still belong in a controlled disposition workflow.
A practical inventory usually includes:
- Voice systems: PBX units, voicemail appliances, SIP gateways, handsets
- Branch gear: Modems, small business routers, managed switches, adapters
- Mobility devices: Corporate phones and wireless communications endpoints
Data center and support infrastructure
Telecom equipment recycling often extends into adjacent rack infrastructure. That includes servers used for communications workloads, storage arrays supporting telecom applications, PDUs, UPS units, cabling, transceivers, and rack-mounted accessories.
Many organizations need one disposition event for all of it, especially during relocations, office closures, and decommissioning projects. That's where broader IT equipment recycling services become relevant, because telecom hardware rarely exits in isolation.
The best inventories aren't theoretical. They reflect what technicians will actually touch during de-racking, disconnects, and loadout.
Legacy systems still count
Older gear creates some of the biggest blind spots. Analog phone systems, older PBX cabinets, discontinued network appliances, and outdated wiring closets may no longer be in active use, but they still require the same discipline. Legacy hardware often sits longest, loses documentation first, and creates the most confusion at pickup time.
If a team can identify all four categories before scheduling removal, the recycling process runs cleaner and the financial picture gets more accurate.
Navigating Data Security and Regulatory Compliance

Factory reset isn't data sanitization. That's the first point I push in any telecom disposition discussion. Routers, servers, PBX systems, and switches can retain logs, credentials, subscriber details, routing tables, and configuration artifacts long after a basic erase.
According to this telecom recycling security guide, secure sanitization requires DoD-compliant wiping or physical destruction such as shredding to less than 2mm, and un-sanitized telecom gear contributes to an estimated 20% of enterprise data leaks from e-waste. That's why disposal has to be treated as a security event, not a hauling event.
What works and what doesn't
Some methods are defensible. Others create false confidence.
| Method | What it does well | Where it fails |
|---|---|---|
| Basic reset | Removes user-facing settings | Doesn't reliably eliminate recoverable data |
| Software wiping | Works when drives are healthy and accessible | Not every telecom device exposes storage cleanly |
| Physical shredding | Strong option for failed or sensitive media | Ends reuse value for that media |
| Degaussing | Useful in the right media context | Not universal across all device types |
For teams dealing with high-risk environments, physical controls matter alongside sanitization. If you're planning staging, movement, or destruction areas, these high security solutions from Material Handling USA are a useful reference for thinking through containment and controlled access.
Compliance is about proof
Regulations don't care that equipment was obsolete. They care whether a business handled information responsibly. The FTC Disposal Rule is part of that conversation. So are sector-specific obligations in healthcare, finance, education, and public agencies. If European personal data passed through the environment, GDPR concerns can also shape destruction standards and documentation requirements.
A strong disposition program usually includes:
- Documented asset identification: Teams know what devices are in scope before anything moves.
- Approved sanitization path: Wipe when reuse is appropriate. Destroy when risk or hardware condition demands it.
- Serialized reporting: Results need to map back to the actual asset list.
- Certificates: Legal and audit teams will ask for them later, not on pickup day.
For Cisco environments, even a task as routine as resetting a Cisco switch shouldn't be mistaken for compliant final disposition. Operational reset and certified data destruction solve different problems.
A secure telecom recycling program doesn't rely on trust. It relies on documented controls, verifiable outcomes, and records that stand up in an audit.
The Step-by-Step Recycling Process and Chain of Custody
The fastest way to lose trust in telecom equipment recycling is to make it a black box. IT directors need to know what happens after pickup, who handles the assets, and what records come back.

From pickup to processing
A professional workflow usually starts with inventory confirmation and site preparation. Equipment is grouped by location, sensitivity, and likely disposition path. Data-bearing assets are separated from simple peripherals. Loose drives, line cards, phones, and small network devices are packaged so they don't disappear into mixed freight.
Once assets leave the site, chain of custody begins in earnest. Each transfer should be documented. Each load should stay tied to a customer record. At the facility, the receiving process matters because that's where discrepancies show up first.
A clean sequence looks like this:
- Collection and logging at the client site
- Transport with documented handoff
- Receiving and serialized intake
- Data sanitization or destruction
- Testing for reuse potential
- Dismantling and material separation
- Final reporting and certificates
Where material recovery happens
After data handling and asset testing, non-reusable telecom gear moves into dismantling. During dismantling, value can either be preserved or lost. According to telecom material recycling processing data, specialized e-scrap lines can process up to 4 million pounds monthly, achieve material recovery rates exceeding 95%, and telecom scrap can contain 2 to 5 times higher precious metal concentrations than consumer electronics.
That matters because telecom gear isn't ordinary scrap. Dense boards, backplanes, transceivers, and cabling often justify careful separation instead of bulk disposal.
If a recycler can't explain how it tracks, tests, dismantles, and reports on telecom assets, you're not looking at a mature chain of custody.
Why chain of custody is operational, not just legal
Good documentation prevents simple problems from becoming major ones. Missing serials, mixed pallets, and vague downstream reporting all create cleanup work for IT, compliance, and finance. A tight chain of custody does the opposite. It gives the organization a defensible record and makes the final disposition report usable.
For teams that want a plain-language overview of downstream processing, this breakdown of what happens to recycled electronics is a practical reference point.
Maximizing Value Recovery Through IT Buyback Programs
A lot of telecom recycling programs leave money on the floor because they start with a scrap mindset. That's usually the wrong first move. The right order is evaluate for reuse, then harvest commodity value from what can't be remarketed.

Two value paths
Functional telecom assets may have secondary market demand. That usually applies to newer switches, enterprise phones, network modules, optics, and branded infrastructure that buyers can still deploy. In those cases, secure wiping, testing, grading, and resale can offset a meaningful part of project cost.
Older or failed gear still has material value. According to BCG's discussion of e-waste recovery, the US loses an estimated $4 billion annually in copper, palladium, and gold in discarded computer equipment, and advanced AI-powered sorting can achieve 95% accuracy and potentially save 15% to 25% in costs. Telecom gear is especially relevant because it often contains high-grade boards and useful metal content.
What affects payout
Not every telecom asset deserves the same disposition path. Value usually turns on a few factors:
- Age and model demand: A supported switch line has a different market than obsolete voice hardware.
- Condition: Missing rails, damaged ports, and corrosion reduce remarketing options.
- Completeness: Power supplies, modules, and matching components help.
- Data handling requirements: Some clients choose destruction paths that intentionally prioritize risk reduction over resale.
That's why a blended model often works best. Some assets go through remarketing. Others go directly to dismantling and metal recovery. For Georgia organizations reviewing local recovery options, IT equipment resale in Georgia is the right lens, because it frames end-of-life gear as an asset class instead of a disposal burden.
Worth remembering: The cheapest quote isn't always the lowest-cost outcome. Poor sorting and rushed scrap handling can erase recoverable value that never shows up on a disposal invoice.
Coordinating Logistics and On-Site De-Installation
Telecom equipment recycling projects often fail before the truck arrives. The issue is rarely the recycler's final processing capability. It's the on-site execution. If technicians can't access the right rooms, if racks aren't clearly in scope, or if active circuits weren't separated from retired hardware, the project gets messy fast.
A common example is a multi-floor office phone migration. The new cloud voice platform goes live, but old handsets, gateways, patching gear, and closet hardware remain scattered across departments. Facilities wants the space back. IT wants nothing unplugged by mistake. Procurement wants the retired assets counted. That isn't just a pickup. It's a coordinated de-installation.
What good field execution looks like
Strong logistics teams start with a site plan. They identify loading access, elevators, security checkpoints, dock constraints, and any after-hours requirements. They also confirm whether the project includes de-racking, cable removal, palletization, or only packed equipment pickup.
On-site de-installation usually goes smoother when teams separate work into layers:
- Active versus retired assets: Nothing moves until ownership confirms it's out of production.
- Rack gear versus loose inventory: De-racking requires different tools and more time than boxed pickups.
- Cabling scope: Some clients want only hardware removed. Others want the room stripped back.
- Multi-site timing: Branch offices, clinics, and remote locations need sequencing, not guesswork.
Where projects usually break down
The weak point is often handoff between departments. IT may know what's retired, but facilities controls access. Procurement may hold the asset list, but operations decides timing. If those groups don't align, technicians arrive to partial inventories and last-minute changes.
That's why experienced providers push for a pre-move review. It isn't bureaucracy. It's how you avoid disconnecting live infrastructure, leaving high-value gear behind, or paying crews to wait while teams sort ownership questions on the floor.
For larger telecom refreshes, logistics planning should be treated like a migration workstream with tasks, approvals, and closeout records.
The Importance of Audits and Certificates for Compliance
A recycler's verbal assurance has almost no value during an audit. What matters is the paper trail. If a company can't show what was collected, how it was handled, and how data was destroyed, then the disposition process isn't fully defensible.
The documents that matter
Most business clients should expect two core records after telecom equipment recycling. One is the certificate showing the equipment was processed through an approved recycling stream. The other is the certificate showing data-bearing media was sanitized or destroyed according to the agreed method.
Those records should map back to the original inventory in a way an internal auditor can follow. If the documentation is too vague, it creates more work than it saves.
A solid file usually includes:
- Pickup documentation: What left the site, when, and under whose custody
- Asset-level records: Especially for serialized network and server equipment
- Destruction reporting: The method used for drives or embedded storage
- Final certificates: Documents legal, procurement, and compliance teams can retain
Why third-party standards matter
Industry certifications give buyers an external benchmark. They don't replace diligence, but they do show that the processor operates against formal standards for environmental management, worker safety, and data security controls.
The certificate itself is the endpoint of a larger discipline: inventory control, custody records, secure handling, and downstream accountability. Without those pieces, a certificate is just a document. With them, it's evidence.
For teams that need to understand what a formal destruction record should cover, this overview of a certificate of destruction is a practical reference.
Audit-ready telecom recycling isn't about generating more paperwork. It's about producing the specific records that prove your company handled retired assets responsibly.
How to Evaluate and Choose a Telecom Recycling Partner
According to IBISWorld's electronic goods recycling industry data, the U.S. industry includes 863 businesses and is projected to reach $28.1 billion in revenue. A market that large gives IT teams plenty of options, but it also increases the odds of selecting a vendor that can collect equipment without meeting your standards for security, reporting, or value recovery.
The right partner reduces operational risk and internal workload. The wrong one creates audit gaps, weak asset visibility, and missed resale value that never shows up on a spreadsheet because the equipment was scrapped too early.
The shortlist questions that expose real capability
Good vendor evaluation starts with process discipline, not marketing claims. Ask for specifics, and pay attention to how clearly the provider explains exceptions, not just the happy path.
- What certifications do you maintain: A qualified recycler should name them directly and explain how those standards show up in day-to-day handling.
- How do you process data-bearing telecom devices: Look for a defined method for sanitization or destruction, plus reporting that ties back to individual assets where appropriate.
- How do you track assets from pickup through final disposition: The answer should cover intake controls, serialized tracking, handoffs, and final reporting.
- How do you decide what gets resold versus scrapped: Providers that test and grade equipment before recycling often return better financial results.
- Can you handle de-installation, palletization, and multi-site pickups: This matters if your telecom refresh spans branches, MDF and IDF closets, call centers, or data rooms.
A capable partner should also be comfortable speaking with IT, procurement, compliance, and facilities in the same project. That is usually where weak operators start to break down.
Red flags worth noticing
Some problems show up during the RFP process. Others appear only after pickup is scheduled.
| Green flag | Red flag |
|---|---|
| Clear asset-level reporting | Generic weight-only reporting |
| Defined sanitization or destruction methods | "We erase everything" with no method or evidence |
| Project scoping before pickup | Last-minute scheduling with little site planning |
| Triage for reuse, resale, and scrap | Defaulting everything to scrap |
| Direct answers about downstream vendors | Evasive answers about where material goes |
One red flag matters more than it first appears. If a recycler cannot explain how they separate reusable telecom gear from commodity scrap, your company may lose both money and defensibility. Finance loses recovery value. Compliance loses transparency.
What a strong partner should deliver
A strong telecom recycling partner should make your internal process easier to govern. That means clear scoping, documented handoffs, realistic scheduling, and reporting your team can hand to auditors without rebuilding the file.
The key decision point is not who can haul equipment away. Many companies can do that. The better question is who can protect data, preserve chain-of-custody integrity, identify resale opportunities before destruction, and return records your legal, procurement, and compliance teams can use.
If you are comparing vendors in Atlanta, use that standard. It eliminates weak options quickly and helps you choose a partner that supports risk reduction, value recovery, and audit readiness in the same engagement.



