When a telecom refresh is finished, the old gear usually sits in racks, cages, and storage rooms longer than anyone planned. Routers, switches, base-station components, PBX cards, optics, and spares still have value, but only if someone turns a pile of hardware into a documented, marketable asset lot. For enterprise teams trying to sell used telecom equipment for cash, that gap between “we replaced it” and “we got paid” is where most value leaks out.
The process looks simple from a distance. It isn’t. Equipment has to be identified correctly, storage media has to be handled securely, buyer terms have to be compared carefully, and logistics have to be controlled so the final net recovery matches the original quote. If you're managing decommissioned gear in Atlanta, Georgia or coordinating a multi-site rollout elsewhere, the same rule applies. Treat resale as an asset recovery project, not a cleanup task.
The Untapped Value in Your Decommissioned Telecom Gear
A lot of organizations still think used telecom hardware belongs in the recycling queue the moment it leaves production. That’s usually the wrong first move. Secondary demand for business-grade networking and telecom gear is large, active, and increasingly formal.
The market itself proves the point. The global refurbished networking equipment market was valued at USD 145.5 billion in 2024 and is projected to grow to USD 170.52 billion by 2033, according to Beyond Surplus on the refurbished networking equipment market. That tells enterprise sellers something important. Used telecom resale isn't fringe activity. It’s part of a mature procurement and remarketing ecosystem.

What still has resale potential
Not every asset belongs in the same bucket. Buyers typically separate gear into reusable systems, refurbishable units, parts-harvest candidates, and scrap.
Common value-bearing categories include:
- Core network hardware: Enterprise routers, switches, firewalls, and chassis.
- Telecom infrastructure: PBX components, voice systems, BTS and RBS equipment, and carrier-grade modules.
- Field-replaceable parts: Power supplies, line cards, transceivers, and interface modules.
- Complete configured lots: Matched systems with rails, cables, modules, and documentation.
Practical rule: The more complete and verifiable the equipment package is, the easier it is for a buyer to resell, refurbish, or redeploy it.
That’s why businesses that want to recover value usually start with a resale path, then move non-usable residuals into recycling. For companies with regional inventory or Georgia-based facilities, a structured IT equipment resale process in Georgia can keep recoverable assets out of the scrap stream and convert dormant hardware into budget relief.
Preparing Your Telecom Assets for a High-Value Sale
Buyers don’t pay top value for vague descriptions like “Cisco gear, mixed lot, good condition.” They pay for specificity. The first job is building an inventory that removes uncertainty.

Build a buyer-ready manifest
A working spreadsheet is enough if it’s thorough. For each asset, capture:
- Manufacturer and family: Cisco ASR, Juniper MX, Ericsson RBS, Avaya, Nortel, Huawei, or similar.
- Exact model number: Not just product family. Buyers need the precise chassis or module identifier.
- Serial number: This helps with traceability, age checks, and internal chain-of-custody.
- Quantity: Group like units, but don’t blur different revisions into one line item.
- Configuration details: Installed line cards, supervisors, power supplies, fan trays, optics, and licenses if available.
- Physical condition: Clean, scratched, dented, rack rash, missing faceplates, broken tabs.
- Functional status: Pulled working, powers on, untested, damaged, or parts only.
- Site location: Critical when the inventory spans multiple rooms, offices, or data centers.
A serious buyer reads this list as a risk document. If details are missing, they assume the worst and price accordingly.
Photograph what matters
Photos aren’t decorative. They answer questions before the quote stage. Use clear images of the front, rear, ports, labels, and any installed modules. If internal boards or field-upgradable parts are relevant, photograph those too.
A strong photo set should show:
- Front chassis condition
- Rear ports and power configuration
- Model and serial labels
- Installed cards or modules
- Any visible damage or missing components
Missing visual proof often turns a reusable asset into an “untested bulk lot” in the buyer’s system.
Separate data-bearing from non-data-bearing assets
Telecom environments often mix switching hardware, voice systems, appliances, and storage-adjacent devices in the same lot. Don’t inventory everything as if it carries the same risk profile. Some devices need sanitization before they leave the site. Others don’t.
This is also the right time to check operational settings before disposition. If your team needs a reference for network device turnover, guidance on resetting Cisco switches is useful for understanding how organizations prepare certain equipment before transfer, testing, or redeployment.
Package the lot like a commercial transfer
Once the manifest is complete, match the paperwork to the floor. Label pallets or shelves to correspond with line items. Keep loose transceivers, rails, and power cords grouped with the parent system where possible. Don’t leave buyers to guess which accessory belongs to which chassis.
A simple internal handoff checklist helps:
| Item | Why it matters |
|---|---|
| Manifest finalized | Prevents quote disputes |
| Photos attached | Reduces condition uncertainty |
| Accessories grouped | Preserves system value |
| Locations mapped | Speeds pickup planning |
| Sensitive devices flagged | Keeps compliance separate from resale |
Companies lose value here by moving too fast. They stack mixed gear onto pallets, toss loose modules into boxes, and call it liquidation. That approach creates confusion, lowers trust, and invites broad discounting.
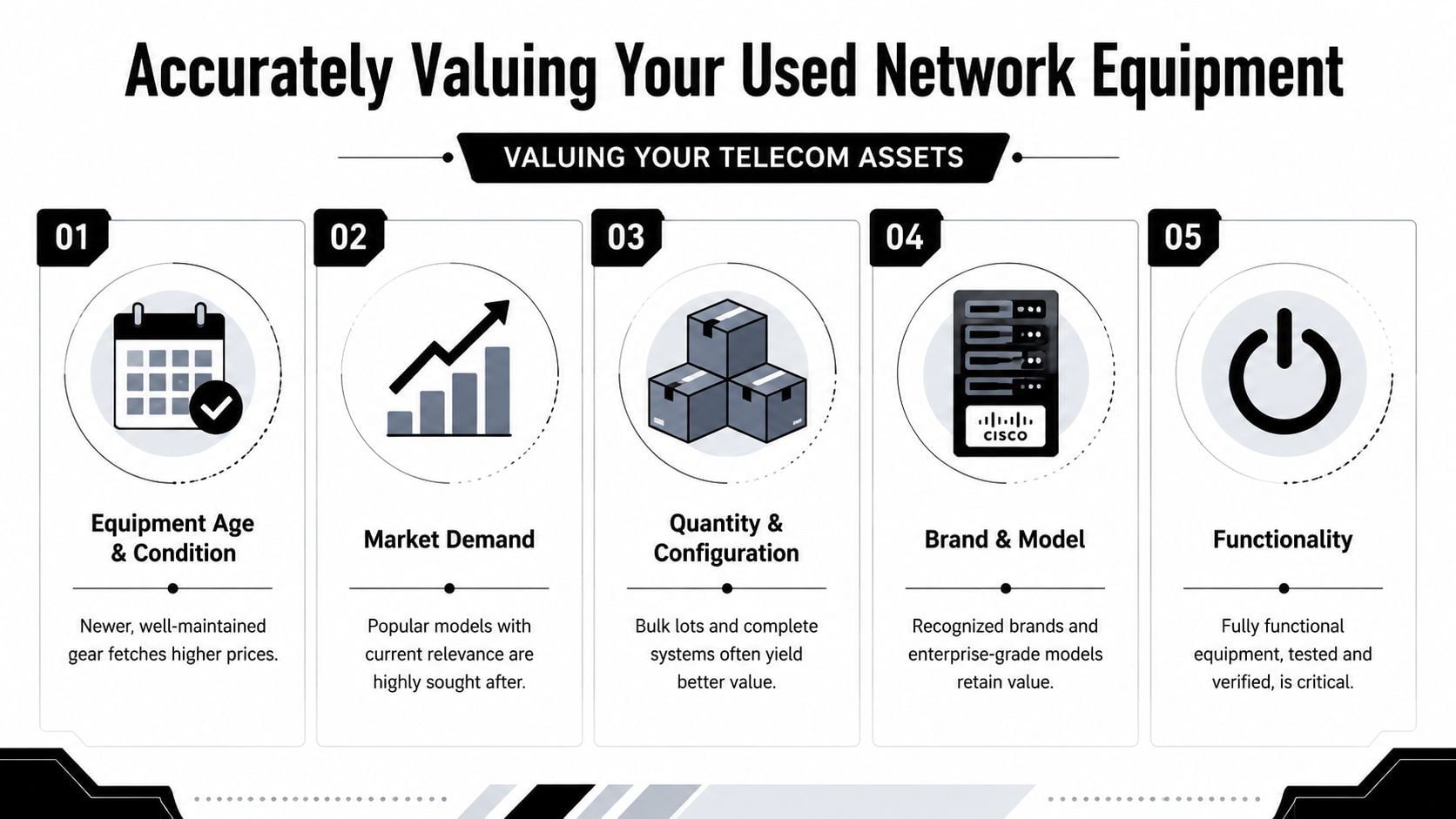
Accurately Valuing Your Used Network Equipment
Valuation isn’t about guessing what the gear “should be worth.” It’s about reducing uncertainty until buyers can price the lot as resale inventory instead of operational risk.
Why one offer usually underperforms
A common mistake is accepting the first buyback number because it feels efficient. It rarely is. Industry data shows that a structured valuation process, including soliciting 3 to 5 formal quotes from ITADs or specialized buyers, can help sellers realize 40–70% of the original list price, compared to 10–25% for ad hoc sales. Businesses that request multiple quotes recover, on average, 23% more revenue than those who accept the first offer, according to Carritech’s guidance on selling used telecommunications equipment.
That difference comes from process, not luck. Buyers price aggressively when the seller presents a vague lot, limited documentation, or a short deadline. They compete harder when the inventory is clean, the terms are clear, and they know they’re one of several bidders.
What drives value up or down
The same chassis can produce very different offers depending on how it’s presented. Buyers usually look at the following in combination:
- Configuration completeness: A chassis with matching cards and power supplies is easier to remarket than a stripped frame.
- Testability: “Pulled from working environment” is better than “unknown,” but documented test results are even stronger.
- Current demand: Some models move quickly in the secondary market. Others sit.
- Licensing and included components: Missing transceivers, dongles, or key modules can change the buyer’s route from resale to parts harvest.
- Cosmetic condition: This won’t matter equally for every channel, but visible damage narrows the buyer pool.
Buyers don’t pay for possibility. They pay for confidence.
Run a formal RFQ instead of an informal conversation
A structured request for quote should include the manifest, photo package, pickup location, lot terms, and whether the offer should assume tested resale, as-is purchase, or mixed recovery. A telecom-focused partner can add real discipline to this process. Teams that need a formal outlet often use telecom equipment liquidation services to centralize inventory review, market outreach, and disposition planning.
Use a simple comparison sheet when offers come back:
| Buyer | Scope included | Pricing basis | Inspection adjustment terms | Shipping responsibility | Payment timing |
|---|---|---|---|---|---|
| Buyer A | Full lot | Unitized | Defined | Buyer | Stated in agreement |
| Buyer B | Partial lot | Bulk | Broad discretion | Seller unclear | Not clearly stated |
| Buyer C | Full lot | Unitized plus parts | Defined | Buyer | Stated after inspection |
The highest top-line number isn’t always the best quote. If the inspection adjustment language is vague, the pickup terms are undefined, or the buyer excludes accessories that were assumed to be included, your net recovery can shrink fast.
Ensuring Secure Data Destruction and Full Compliance
Resale value matters. Liability matters more. Telecom equipment often touches call logs, credentials, configurations, user directories, voicemail data, and network information that your organization can’t afford to release.

Treat sanitization as liability transfer
If a device stores data, sanitize it before resale or ensure the downstream partner documents that process under contract. That applies to more than servers. Telecom systems, unified communications platforms, security appliances, and certain network devices may all contain recoverable information.
There are usually two disposition paths:
- Software-based sanitization: Appropriate when the asset remains reusable and supported wiping methods fit the device type.
- Physical destruction: Appropriate when reuse isn’t viable, media can’t be reliably sanitized, or policy requires irreversible destruction.
What matters most is documented execution. A certificate of data destruction and a clear chain of custody show who handled the asset, when it changed hands, and what happened to the data-bearing component.
Compliance breaks when assumptions replace evidence
Many internal teams assume a factory reset equals data destruction. It often doesn’t. Others assume a downstream buyer will sanitize equipment automatically. That assumption can become a legal problem if nothing in the agreement says so and no certificate is issued.
For organizations building a formal process, NIST SP 800-88 data sanitization guidance is a useful reference point for deciding when wiping, purging, or destruction is appropriate.
If you can't prove how the data was destroyed, you haven't closed the risk.
A practical outside read on prevention and governance is Safeguarding your business from data breaches. It’s a good reminder that breach prevention isn’t only about active systems. It includes retired hardware, handoffs, and disposal decisions.
Ask these compliance questions before release
Before any pickup happens, your legal, security, or IT operations team should be able to answer:
- Which assets contain data or credentials
- Who performs sanitization
- What standard or method is used
- What documentation is issued
- When custody transfers
- How exceptions are handled if a device can’t be sanitized for resale
That list sounds administrative until an auditor asks for evidence. Then it becomes operationally critical. Companies usually regret two shortcuts here. Letting mixed lots leave without media segregation, and relying on generic recycling paperwork that doesn’t identify the actual sanitization outcome.
Finding the Right Buyer for Your Telecom Portfolio
Buyer selection changes the entire transaction. The wrong channel creates more admin, more delay, and more uncertainty than the recovered cash justifies.

Compare the common routes
For enterprise sellers, the usual options are ITAD vendors, telecom brokers, online marketplaces, and recycling-only outlets. Each can work, but not for the same situation.
| Buyer type | Best fit | Main upside | Main trade-off |
|---|---|---|---|
| ITAD provider | Enterprise lots with security and documentation needs | Integrated logistics, compliance support, resale recovery | May apply stricter intake process |
| Telecom broker | Specialized telecom inventory with active niche demand | Access to targeted buyers | More coordination may stay with seller |
| Online marketplace | Small quantities or very specific items | Direct listing control | High effort, inconsistent buyers, more risk |
| Recycling outlet | Non-salvageable gear | Fast removal of low-value material | Minimal financial recovery |
When full-service support makes sense
Most enterprise clients don’t need a listing platform. They need a controlled business process. That includes inventory validation, data handling, pickup scheduling, inspection terms, and final reporting. A qualified ITAD vendor often becomes the lowest-friction option because one party coordinates the handoff from floor to settlement.
If you’re screening buyers, start with telecom surplus buyers that understand business-grade voice and network equipment rather than general used electronics purchasers.
One example in this category is Beyond Surplus, which buys used telecom equipment and supports pickup, secure disposition, and documentation for business customers. That kind of model is useful when the seller wants one contract covering logistics, value recovery, and chain of custody.
Red flags during buyer review
The problems usually show up before the equipment moves. Watch for:
- Loose inspection language: If the buyer can reprice broadly after pickup, the initial quote may not mean much.
- No data handling detail: If they can’t explain sanitization responsibility, stop there.
- Undefined logistics: Pickup windows, packaging expectations, and freight responsibility should be written down.
- Generic bulk offers: If they don’t ask for model detail, they’re probably pricing defensively.
A buyer who asks precise questions usually prices more precisely too.
That’s the core trade-off. Open marketplaces can occasionally produce a strong sale on a single in-demand item. They’re rarely efficient for enterprise portfolios with compliance requirements and mixed asset conditions.
Managing a Seamless Transaction from Negotiation to Pickup
Once you’ve selected a buyer, the financial outcome depends on the service agreement and the handoff process. Teams often focus on unit price and miss the terms that control net recovery.
Negotiate the deal behind the quote
The purchase price matters, but these points often matter just as much:
- Shipping responsibility: Confirm whether pickup, packing, freight, and special handling are included.
- Inspection process: Define what can trigger a price adjustment and what evidence is required.
- Payment timing: Confirm when the payment clock starts. On pickup, on receipt, or after inspection.
- Title transfer: Make sure both sides know when ownership and liability change.
- Exclusions: Spell out whether rails, optics, cables, or licenses are included.
One of the clearest issues in enterprise liquidation is timing. Many businesses are surprised by realistic payment timelines and the effect of bulk volume on per-unit pricing. It is advisable to clarify upfront whether shipping is fully covered and how long payment will take post-inspection, as these factors significantly impact the true net recovery beyond the initial quote, as noted by Telecom Recycle on excess telecom equipment.
Plan the pickup like an operations event
A smooth pickup starts long before the truck arrives. Stage pallets by site or room, label them to match the manifest, and identify any access constraints such as elevators, loading docks, security windows, or badging requirements.
For logistics teams that want a practical overview of handoff variables, Snappycrate's delivery insights are useful because they highlight the kinds of pickup and delivery details that affect timing, coordination, and condition on arrival.
Use a short release checklist:
- Match pallets to manifest
- Separate data-bearing exceptions
- Photograph staged loads
- Record carrier and pickup time
- Get signed transfer paperwork
Prevent avoidable end-of-deal disputes
Most disputes come from mismatched expectations. The seller thought freight was included. The buyer expected gear to be palletized. The inspection team found missing modules that weren’t listed as absent. None of this is unusual. All of it is preventable.
A clean transaction usually has three traits. The manifest is specific, the commercial terms are written in plain language, and someone on the seller’s side owns the handoff through payment receipt.
If you're trying to sell used telecom equipment for cash at enterprise scale, speed alone shouldn't be the goal. Controlled execution should be. A fast but sloppy handoff can erase value through deductions, delays, or compliance gaps.
Conclusion Your Strategic Path to Asset Recovery
The companies that recover the most from retired telecom hardware don’t treat disposition as a side task. They run it like a controlled asset recovery program. That means documenting the inventory at the component level, routing data-bearing assets through a defensible sanitization process, comparing buyers on terms as well as price, and managing pickup as a formal custody transfer.
A loose approach usually creates the same problems every time. Vague manifests attract broad discounts. Mixed pallets create inspection issues. Incomplete configurations lower resale potential. Undefined payment terms slow down cash recovery. By the time the transaction closes, the original “good offer” doesn’t look so good.
The better approach is more disciplined but far less risky. Keep complete kits together when possible. Separate reusable telecom assets from true end-of-life material. Ask for formal quotes, not casual estimates. Review adjustment clauses before anything leaves the building. Make documentation part of the deliverable, not an afterthought.
That combination does more than protect compliance. It improves financial outcomes because buyers can price a clear, lower-risk opportunity. In practice, that’s what professional partnership is really for. Not just moving boxes, but reducing uncertainty from the first inventory pass through final settlement.
If your team has aging routers, PBX gear, voice infrastructure, or carrier equipment sitting idle, there’s a practical path forward. Recover value where the market supports it. Recycle only what no longer belongs in the resale stream. And make sure every asset leaves under terms your finance, IT, and compliance teams can defend.
Contact Beyond Surplus to evaluate surplus telecom hardware, coordinate secure pickup, and build a documented ITAD process that protects data while improving net recovery.