Staring at a pile of old hard drives and servers? You're looking at a stack of unlocked filing cabinets. Each device is a potential data breach waiting to happen, a disaster that could cost your Colorado business millions in fines and shatter its reputation. This is why secure Colorado data destruction isn't just an IT chore—it's a critical business strategy for every IT manager, facility manager, and business owner.
Why Secure Data Destruction is Non-Negotiable in Colorado

In today's regulatory landscape, businesses cannot afford to be careless with end-of-life IT assets. Regulations like the Colorado Privacy Act (CPA) and federal mandates such as HIPAA have significantly raised the stakes. Simply hitting "delete" or letting old equipment pile up in a storage closet is no longer a compliant option. Each retired server, laptop, and hard drive is a ticking liability until its data is permanently and verifiably destroyed.
The legal framework in Colorado is particularly stringent, demanding proactive data protection from every commercial organization. Businesses are legally responsible for protecting sensitive information throughout its entire lifecycle, from creation to final disposal. That responsibility doesn't end when a device is retired; in fact, that is often when the greatest risk begins.
The Legal Imperative for Colorado Businesses
Colorado has established clear rules for how businesses must handle sensitive data. Specifically, Colorado House Bill 18-1128 requires organizations to implement and maintain reasonable security procedures, which explicitly includes the secure destruction of personal information when it is no longer needed. The law mandates a written policy for destroying documents containing personally identifiable information (PII) and clarifies that destruction methods must render the data completely unreadable and indecipherable.
Failure to comply can lead to staggering financial penalties and the kind of reputational damage that takes years to repair. A single data breach can erode the customer trust you've worked hard to build, impacting your bottom line long after the incident fades from headlines.
A proactive data destruction strategy is more than a compliance checkbox; it is a fundamental component of modern risk management. It protects your customers, your employees, and your brand's integrity.
Moving Beyond Simple Deletion
A common misconception is that formatting a hard drive is sufficient for data removal. It is not. Data recovery software can often retrieve information from formatted or wiped devices, leaving your company completely exposed. Certified data destruction ensures this cannot happen. The true importance of secure data destruction lies in its finality and verifiability.
Engaging a professional service provides critical assurances through:
- Guaranteed Data Elimination: Methods like physical shredding obliterate storage media, making data recovery impossible.
- Proof of Compliance: You receive a Certificate of Data Destruction, a legal record proving due diligence and transferring liability.
- Enhanced Security: It prevents sensitive corporate intelligence, client lists, and financial records from ever falling into the wrong hands.
Ultimately, investing in professional Colorado data destruction is a strategic business decision that protects your company's future. It converts a potential liability into a verified, secure, and compliant process.
Understanding Colorado's Data Disposal and Security Laws
Navigating the complex web of data destruction regulations can be overwhelming, but for any business operating in the Centennial State, compliance is non-negotiable. Failure to adhere to these laws not only exposes an organization to significant fines but can also severely damage its reputation. The first step toward a robust and defensible IT Asset Disposition (ITAD) plan is understanding the specific legal framework governing Colorado data destruction.
At the center are two major state laws: the Colorado Privacy Act (CPA) and House Bill 18-1128. Together, they impose a clear duty on businesses to protect the Personally Identifiable Information (PII) of Colorado residents, from collection to final disposal. PII is defined broadly, covering everything from a name paired with a Social Security number to financial account details. Your legal obligation is to ensure this data becomes completely unreadable and unrecoverable once there is no longer a legitimate business purpose for its retention.
The Colorado Privacy Act and Its Impact
The Colorado Privacy Act (CPA) grants consumers significant control over their personal data, including the right to have it deleted. This directly impacts your data destruction processes. When a customer exercises their right to deletion, you must have a bulletproof system to permanently eradicate their information from all systems—including legacy hard drives, backup tapes, and decommissioned servers.
Regulations are continually evolving. Starting July 1, 2025, the Biometric Data Privacy Amendment to the CPA will take effect, adding even stricter requirements for handling sensitive data like fingerprints or facial scans. The trend is clear: Colorado's data protection laws are strengthening, placing greater responsibility on businesses to securely manage the entire data lifecycle.
Federal and Industry-Specific Regulations
In addition to Colorado's state-level laws, businesses must also comply with a range of federal and industry-specific regulations. These rules create overlapping layers of compliance that necessitate a comprehensive strategy.
Key federal regulations include:
- The FTC Disposal Rule: This federal rule mandates that businesses take appropriate measures to dispose of sensitive information derived from consumer reports, setting a national baseline for secure destruction.
- HIPAA (Health Insurance Portability and Accountability Act): Healthcare organizations are required by HIPAA's privacy and security rules to securely and permanently destroy Protected Health Information (PHI) on all electronic media.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions are bound by GLBA to safeguard consumers' private financial information, which includes strict protocols for the disposal of customer records.
The penalties for non-compliance are severe, ranging from substantial fines to legal action. This multi-layered legal landscape makes partnering with a certified ITAD vendor a critical risk management strategy. For more details, see our guide on responsible Colorado electronics recycling services that operate in full alignment with these strict data security standards.
The convergence of state, federal, and industry laws means that a single retired hard drive could fall under multiple regulatory umbrellas. A compliant data destruction program must satisfy the most stringent requirements applicable to your business.
To understand the high standard for compliance, consider the state government's own policy. Colorado's Policy P-104A, the Data Destruction and Computer/Other Electronic Media End-of-Life Policy, sets a high bar for public agencies. It mandates that all data on state-owned media must be completely erased or physically destroyed before the equipment is surplussed, transferred, or discarded, requiring a certificate for every device. You can review the state's rigorous standards in the official policy document.
Below is a compliance checklist to help your business navigate these complex requirements.
Colorado Data Destruction Compliance Checklist
This table summarizes key legal requirements and best practices for businesses in Colorado, ensuring your data disposal methods are compliant.
| Requirement Area | Key Action Required | Relevant Regulation(s) |
|---|---|---|
| PII Protection | Implement and maintain a written policy for the destruction of PII. | HB 18-1128, Colorado Privacy Act (CPA) |
| Consumer Rights | Establish a process to honor consumer requests for data deletion. | Colorado Privacy Act (CPA) |
| Secure Disposal | Ensure PII is rendered unreadable and unrecoverable before disposal. | HB 18-1128, FTC Disposal Rule |
| Healthcare Data | Securely destroy all electronic Protected Health Information (PHI). | HIPAA |
| Financial Data | Properly dispose of customer financial records to prevent unauthorized access. | GLBA |
| Proof of Destruction | Obtain and retain Certificates of Destruction for all disposed media. | Industry Best Practice, P-104A (State Gov) |
| Biometric Data | Comply with specific consent and deletion schedules (effective July 1, 2025). | CPA Biometric Data Amendment |
Following this checklist is an excellent first step, but a truly secure process often requires a partnership with certified data security experts.
Ultimately, building a robust data destruction plan is about more than avoiding fines. It is about protecting your customers, safeguarding your reputation, and ensuring your business operates on a foundation of trust and security.
Choosing the Right Data Destruction Method for Your Assets
Once your Colorado business understands its legal obligations for data disposal, the next critical question is how to execute it. The method of destruction is as crucial as the decision to destroy. Selecting an inappropriate method can leave your organization as exposed as doing nothing at all.
The right destruction method depends on the asset's type, its condition, and its intended end-of-life pathway—whether that is value recovery, recycling, or complete obliteration.
There are three industry-standard methods, each serving a specific purpose.
Data Wiping Digital Sanitization
Data wiping, or sanitization, is a software-based method that systematically overwrites all data on a storage device with random characters. This process buries the original information, making it practically impossible to recover with standard tools. Professionals adhere to strict standards, such as the NIST 800-88 guidelines, which define protocols for media sanitization.
This is the ideal choice for functional IT assets intended for resale, internal redeployment, or donation. By keeping the hardware intact, data wiping allows businesses to recover value from retired equipment while maintaining full compliance with data privacy laws.
- Best For: Functional hard drives (HDDs), solid-state drives (SSDs), laptops, and servers planned for reuse.
- Key Advantage: Preserves the asset for reuse, benefiting IT budgets and sustainability goals.
- Limitation: Not viable for damaged or non-functional drives, as the software cannot run on them.
Degaussing Magnetic Field Erasure
Degaussing is a more intensive process that exposes magnetic storage media to a powerful magnetic field. This scrambles the magnetic domains on a hard drive's platters or a tape's surface, rendering the stored data unreadable. The erasure is total and permanent.
While highly effective for older magnetic media, degaussing is becoming less relevant for modern IT infrastructure. Its primary limitation is that it has no effect on solid-state drives (SSDs), which do not use magnetic storage. This restricts its use to specific legacy hardware.
Degaussing renders the hard drive itself unusable, so it is a destructive method intended only for end-of-life media that will not be reused.
Physical Destruction The Ultimate Guarantee
When an absolute, ironclad guarantee of data elimination is required, nothing surpasses physical destruction. This typically involves shredding. An industrial-grade shredder grinds hard drives, SSDs, backup tapes, and other media into small, confetti-like fragments. The process obliterates the storage platters or flash memory chips, making data reconstruction physically impossible.
For a detailed look at this service, learn more about Beyond Surplus’s approach to secure data destruction and hard drive shredding.
Shredding is the only guaranteed method for destroying data on SSDs and non-functional drives. Because SSDs store data on microscopic flash memory chips, software wiping can sometimes miss data in non-addressable areas. Shredding eliminates this risk entirely by destroying the hardware itself.
This decision-making process helps Colorado businesses navigate their legal responsibilities for protecting PII and other sensitive information.
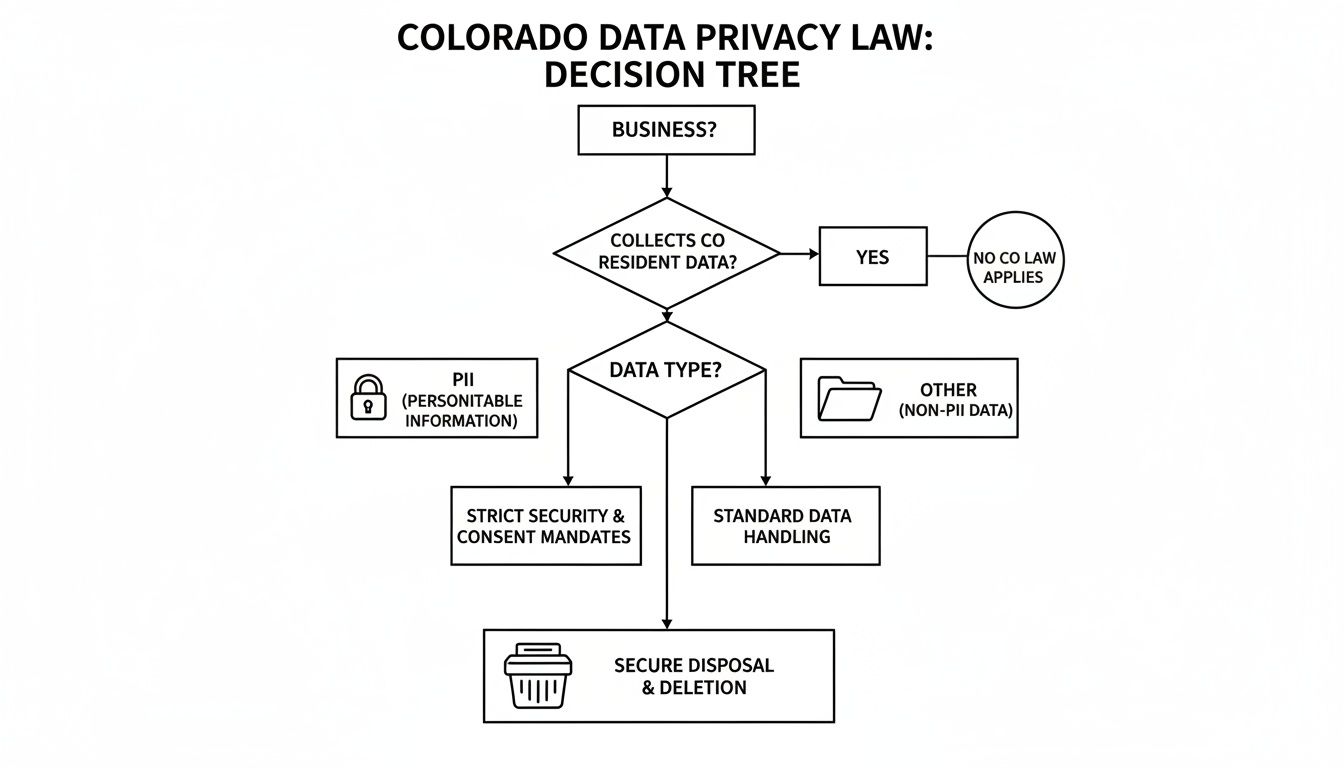
This flowchart reinforces the critical point: regardless of the data type, secure disposal is the final, non-negotiable step for all business assets.
Ultimately, data destruction should be integrated into a comprehensive Information Technology Asset Management (ITAM) strategy. A robust ITAM program ensures security is embedded from procurement through final disposition, leaving no gaps where data could be exposed. Aligning your destruction method with your asset management goals creates a seamless, secure, and compliant end-of-life process.
On-Site vs. Off-Site Hard Drive Shredding Services

A key decision in your Colorado data destruction plan is where the destruction occurs. The choice between on-site and off-site services impacts your security protocols, logistics, and budget. Both methods are secure when performed by a certified vendor, but they cater to different business needs.
On-site shredding, or mobile shredding, brings the destruction process to your location. A specialized truck equipped with an industrial-grade shredder arrives at your facility, allowing you to witness the destruction of your hard drives and other assets firsthand.
The alternative is off-site shredding, also known as plant-based destruction. A certified vendor collects your assets in locked containers, transports them in GPS-tracked vehicles, and destroys them at a secure, monitored facility. This is often an efficient option for large-scale projects.
The Case for On-Site Mobile Shredding
The primary reason to choose on-site shredding is immediate, verifiable proof of destruction. For businesses in highly regulated industries like healthcare (HIPAA) or finance (GLBA), witnessing the process is often a compliance requirement.
Your team can escort the hard drives to the truck and observe the entire destruction process. This direct oversight eliminates potential security gaps during transit. The chain of custody is as short as possible: from your data center to the shredder in your parking lot.
When your compliance framework demands an unbroken and verifiable chain of custody from asset to particle, on-site shredding is the definitive solution. It transforms a security process into a witnessed, documented event.
Key benefits of on-site shredding include:
- Maximum Transparency: You see every asset destroyed with your own eyes, leaving no room for doubt.
- Unbroken Chain of Custody: Data never leaves your property intact, eliminating transport-related risks.
- Immediate Peace of Mind: A Certificate of Data Destruction is issued on the spot, instantly closing the compliance loop.
To see how this service works, explore the options for Colorado hard drive shredding services, which can be tailored for this level of security.
The Advantages of Off-Site Plant-Based Shredding
While on-site shredding offers unparalleled transparency, off-site services provide distinct advantages in logistics and cost-effectiveness. Transporting assets to a dedicated, secure facility is often more efficient and affordable, particularly for large volumes of equipment.
This approach is ideal for large-scale projects like data center decommissioning or a company-wide technology refresh generating hundreds of retired drives. The logistics are managed by professionals, freeing up your internal team. They provide secure, locked bins for collection, and sealed, monitored vehicles transport everything to a facility with 24/7 surveillance and strict access controls.
Off-site shredding can also be a more environmentally friendly choice. The controlled environment of a processing plant enables more efficient sorting and recycling of shredded materials, helping you achieve corporate sustainability goals. The key is to select a vendor with NAID AAA or R2v3 certification. They will provide a detailed, auditable chain-of-custody report from pickup to final destruction, ensuring your Colorado data destruction is secure and compliant, even when performed off-site.
Comparing On-Site vs. Off-Site Data Destruction
Deciding between on-site and off-site destruction depends on your organization's specific priorities. Is absolute, witnessed security your primary concern, or are you seeking a cost-effective solution for a large-scale project? This table breaks down the key differences to help you make an informed choice.
| Feature | On-Site Destruction | Off-Site Destruction |
|---|---|---|
| Security & Oversight | Maximum. You witness the entire process, providing irrefutable proof of destruction. The chain of custody is minimal and completely transparent. | High. Performed in a secure, monitored facility by a certified vendor. Relies on a documented and audited chain of custody from pickup to destruction. |
| Best For | Businesses with strict compliance mandates (HIPAA, GLBA), highly sensitive data, or internal policies requiring direct verification of destruction. | Large-scale IT asset disposition, data center decommissioning, and organizations prioritizing cost-efficiency and streamlined logistics for high-volume jobs. |
| Cost | Generally higher due to the dedicated truck, personnel, and time required at your location. | Typically more cost-effective, especially for bulk quantities, as the process is centralized and optimized for efficiency at the plant. |
| Logistics | Requires scheduling the mobile shredding truck and having your team available to oversee the process. Can be disruptive if space or access is limited. | Simpler for you. The vendor handles all transportation logistics. You just need to prepare the assets for pickup in the provided secure containers. |
| Certificate | Issued immediately on-site upon completion of the shredding process. | Issued after destruction at the facility, typically within a few business days. Provided with a detailed report. |
| Environmental Impact | Shredded materials are collected and transported for recycling, but the process is less centralized than at a dedicated plant. | Often more efficient. A dedicated facility can sort and process materials for recycling more effectively, supporting sustainability goals. |
Ultimately, both methods, when performed by a certified professional, offer a secure and compliant way to destroy data. The right choice depends on balancing your security requirements, budget, and logistical capabilities.
Why Vendor Certification and Chain of Custody Matter

For any business in Colorado, the data destruction process is not complete until the documentation is finalized and filed. This paperwork serves as your legal shield, providing definitive proof that you have met all compliance duties and successfully transferred liability.
Without it, you remain exposed to regulatory scrutiny and potential legal challenges.
Choosing a partner for Colorado data destruction is a critical business decision. You are not just hiring a service; you are entrusting a vendor with your company's most sensitive information. This is where certifications and a robust chain of custody become essential risk management tools. They provide a clear, auditable trail from the moment your equipment leaves your facility to its final, secure destruction.
The Certificate of Data Destruction: Your Legal Safeguard
A Certificate of Data Destruction (CoD) is more than a receipt. It is a legally binding document that serves as your official record of compliant data disposal. For IT leaders and procurement managers, this certificate is the final component that closes the loop on the IT asset disposition (ITAD) process. It is your tangible proof of responsible action.
To be a valid legal document, a CoD must contain specific details that confirm the transfer of liability.
A legitimate certificate will always include:
- Unique Serial Numbers: Every asset, from an individual hard drive to a server, must be listed with its unique serial number for precise tracking.
- Method of Destruction: The document must specify exactly how the data was destroyed—whether through shredding, wiping, or degaussing.
- Date and Location: It must record when and where the destruction occurred, creating a clear and defensible timeline.
- Witness Information: The names of the individuals who witnessed and performed the destruction should be included for full accountability.
- Transfer of Custody: The certificate formally transfers ownership and, most importantly, liability from your organization to the ITAD vendor.
The Power of NAID AAA and R2v3 Certifications
How can you verify that a vendor's process is as secure as they claim? This is where industry certifications are indispensable. They are not merely logos on a website; they are your guarantee that a vendor has passed rigorous, third-party audits of their security protocols, operational integrity, and environmental practices.
Choosing a certified vendor isn't about adding a layer of bureaucracy. It's about outsourcing your risk to a partner whose entire business model has been vetted against the highest industry standards for security and compliance.
Two of the most critical certifications in the ITAD industry are:
- NAID AAA Certification: This is the gold standard for data destruction. The National Association for Information Destruction (NAID) verifies that a company’s hiring practices, physical security, and destruction processes meet extremely stringent, ongoing requirements.
- R2v3 Certification (Responsible Recycling): While focused on environmental responsibility, the R2v3 standard also contains strict mandates for data security. An R2v3 certified vendor guarantees that your assets are not only securely destroyed but also recycled in an environmentally sound manner.
By partnering with a certified provider for your comprehensive Colorado ITAD services, you create a defensible and auditable paper trail that will satisfy regulators, internal auditors, and key stakeholders. It’s the smartest way to ensure your Colorado data destruction program is secure, compliant, and thoroughly documented from start to finish.
Preparing Your Colorado Business for Physical Risks and Business Continuity
When considering data security in Colorado, many businesses focus on cyber threats. However, the state's unique geography presents significant physical risks, including fast-moving wildfires, destructive hail storms, and sudden flash floods.
These events are not abstract possibilities; they are direct threats to your IT infrastructure, data centers, and physical storage media. A robust IT Asset Disposition (ITAD) strategy is therefore a critical component of your disaster recovery and business continuity planning.
Imagine a wildfire evacuation order is issued for your facility. In the scramble to ensure employee safety, the last thing you want to worry about is a legacy server in a storage closet still holding sensitive client data. Decommissioning and securely destroying outdated equipment long before a disaster removes this liability entirely. It’s not just about clearing space; it’s about neutralizing a physical data breach waiting to happen.
Weaving ITAD into Your Disaster Plan
Viewing your ITAD process as a core component of your business continuity plan is a strategic move to mitigate risk. Your certified data destruction partner becomes a key ally in protecting your organization from threats on all fronts—both digital and physical.
The link between environmental threats and data security is increasingly urgent. The need for secure Colorado data destruction is amplified by the state's escalating natural disasters. From 1980 to 2024, Colorado experienced 76 billion-dollar weather events, including 42 severe storms and 12 major wildfires.
The long-term average was approximately 1.7 such events per year. However, between 2020 and 2024, that rate has accelerated to 4.4 annually, highlighting the growing physical threat to data centers and backup media. You can explore this data further on Colorado's severe weather events on NOAA.gov.
In a disaster scenario, unsecured legacy hardware with unshredded drives can easily survive fires or floods. They become a massive breach exposure sitting in the debris and aftermath. Proactive destruction is the only way to completely neutralize this risk.
Proactive Steps for Physical Data Security
To mitigate these physical risks, integrate them into your ITAD strategy with these practical steps:
Regular IT Asset Audits: Maintain a current inventory of all data-bearing assets and flag equipment that is no longer in use for disposition.
Scheduled Destruction Services: Establish regular pickups with your certified ITAD partner to securely destroy retired assets. This prevents accumulation and reduces liability.
Offsite Backup Verification: Ensure your disaster recovery plan includes secure, geographically separate offsite backups. Regularly test and verify these backups to confirm their viability.
By framing Colorado data destruction as an essential part of business continuity, IT managers and data center operators can build a more resilient and secure organization. It provides peace of mind that when a disaster occurs, your sensitive data has already been permanently and verifiably eliminated, protecting your company from a secondary crisis.
Frequently Asked Questions About Colorado Data Destruction
When planning for the disposal of end-of-life IT equipment, many questions arise. Here are straightforward answers to common inquiries from Colorado businesses regarding secure data destruction and IT asset disposal. The goal is to provide the clarity needed to protect your company's sensitive information.
What Is the Most Secure Method for Destroying Data in Colorado?
For absolute, 100% certainty, physical destruction through shredding is the gold standard. This process goes beyond file deletion to physically demolish the storage platters in hard disk drives (HDDs) and pulverize the memory chips in solid-state drives (SSDs). Once an asset is shredded, data recovery is physically impossible.
While secure data wiping is an effective option for functional drives intended for resale or reuse, shredding is the ultimate solution for eliminating all risk. It is the only foolproof method for damaged devices and modern SSDs, ensuring compliance with the most stringent data destruction standards under Colorado law.
Is a Certificate of Data Destruction Legally Required in Colorado?
While no specific Colorado statute explicitly mandates a "Certificate of Data Destruction," this document is an essential business record for demonstrating compliance. It serves as your legal proof of due diligence, showing you fulfilled your duty of care to securely destroy sensitive information as required by regulations like the Colorado Privacy Act (CPA) and the federal FTC Disposal Rule.
Think of a CoD as your liability shield. It's the official record that formally transfers the responsibility for that data from your company to your certified ITAD vendor. This piece of paper is crucial if you're ever audited and provides a clear, defensible record of your due diligence.
You should only partner with a certified vendor who provides a serialized certificate for every destruction project. Without this documentation, you have no verifiable proof of responsible action, leaving your organization exposed to significant risk.
Can You Service Businesses with Multiple Colorado Locations?
Absolutely. A national ITAD partner with a robust logistics network is equipped to manage data destruction for companies with facilities across Colorado. Whether your business operates in Denver, Boulder, Colorado Springs, or Fort Collins, a coordinated plan is essential for maintaining consistent security standards.
A qualified vendor can manage all logistics to ensure your data destruction protocols are uniform, compliant, and secure across every location. This is typically handled through a single point of contact, simplifying the process and providing clear accountability for your enterprise-wide ITAD program. This approach ensures your entire organization is protected, regardless of the number or location of your facilities.
For certified Colorado data destruction that protects your business from every angle, partner with the experts at Beyond Surplus. We offer secure, compliant, and documented ITAD solutions tailored to your organization's needs. Schedule your secure electronics disposal pickup today.